Access control credentials are often seen as a simple component of a security system — a card, a fob, or a mobile app used to unlock doors.
In reality, credentials are one of the most critical design elements in any … Read more
Genetec Architecture Checklist for Scalable Security Systems (10K–50K Users)
Designing a large-scale security system using Genetec Security Center requires more than just adding servers.
Most performance issues in enterprise deployments come from poor architectural decisions, not hardware limitations.
In this guide, you’ll find a practical Genetec architecture checklist… Read more
Read More »Genetec Security Center Architecture Explained
If you’re working with Genetec Security Center but don’t fully understand how all components interact, you’re not alone.
Many technicians and system integrators configure systems without a clear understanding of the Genetec architecture, which often leads to design issues, … Read more
Read More »20 Reasons why you get access denied
Since access control systems manage entrance into spaces, It grants or denies permission according to specific rules. In this article, I am going to show you 20 reasons why access could be denied.
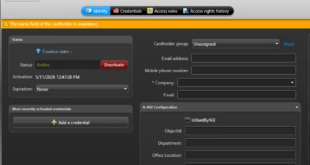
- Unassigned credentials
- Unknown credentials
The physical access … Read more
Read More »Evolution of access control credentials
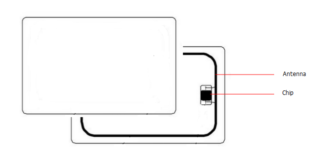
Access control cards have been around for decades. We are used to swiping our cards on a reader, but we are moving toward using our phones, our watches or bracelets to get in.
Access cards technology is constantly evolving, for … Read more
Read More »Cybersecurity maintenance checklist
The following is a CCURE cybersecurity checklist recommendations. They are key practices to protect your system from cybersecurity.
We all know the cyber attacks impacts on our lives. In the IoT era, cybersecurity has become an increasingly vital to government … Read more
Read More »